小弟新来的,分不多,求大神帮忙,先谢了。
先介绍一下背景,有一台笔记本电脑A,进不了win7系统了,每次开机到window画面就重启,用PE启动也是到window画面重启,无法重装系统。但是把硬盘拆了可以用PE启动。(系统都是win7 x64)
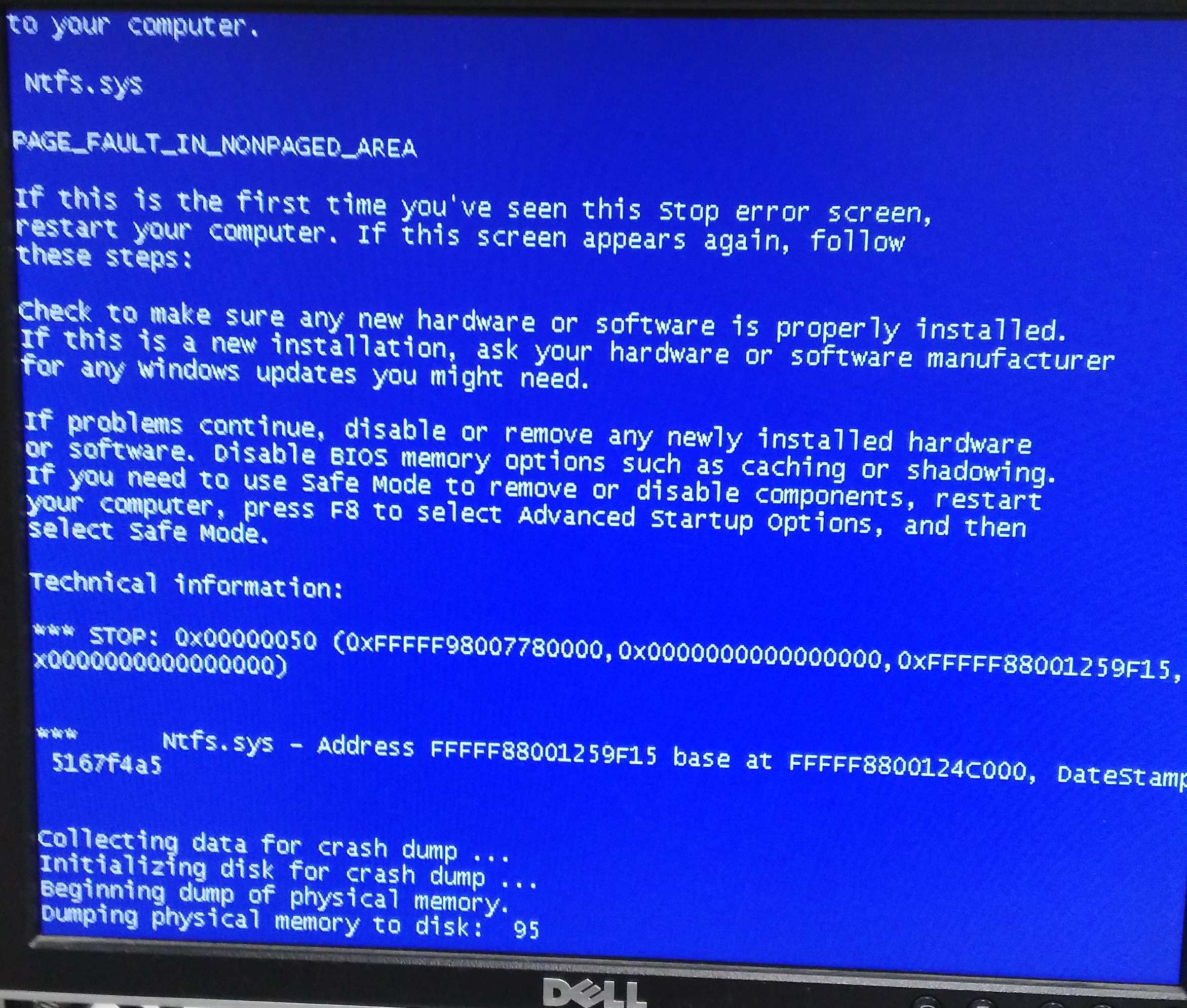
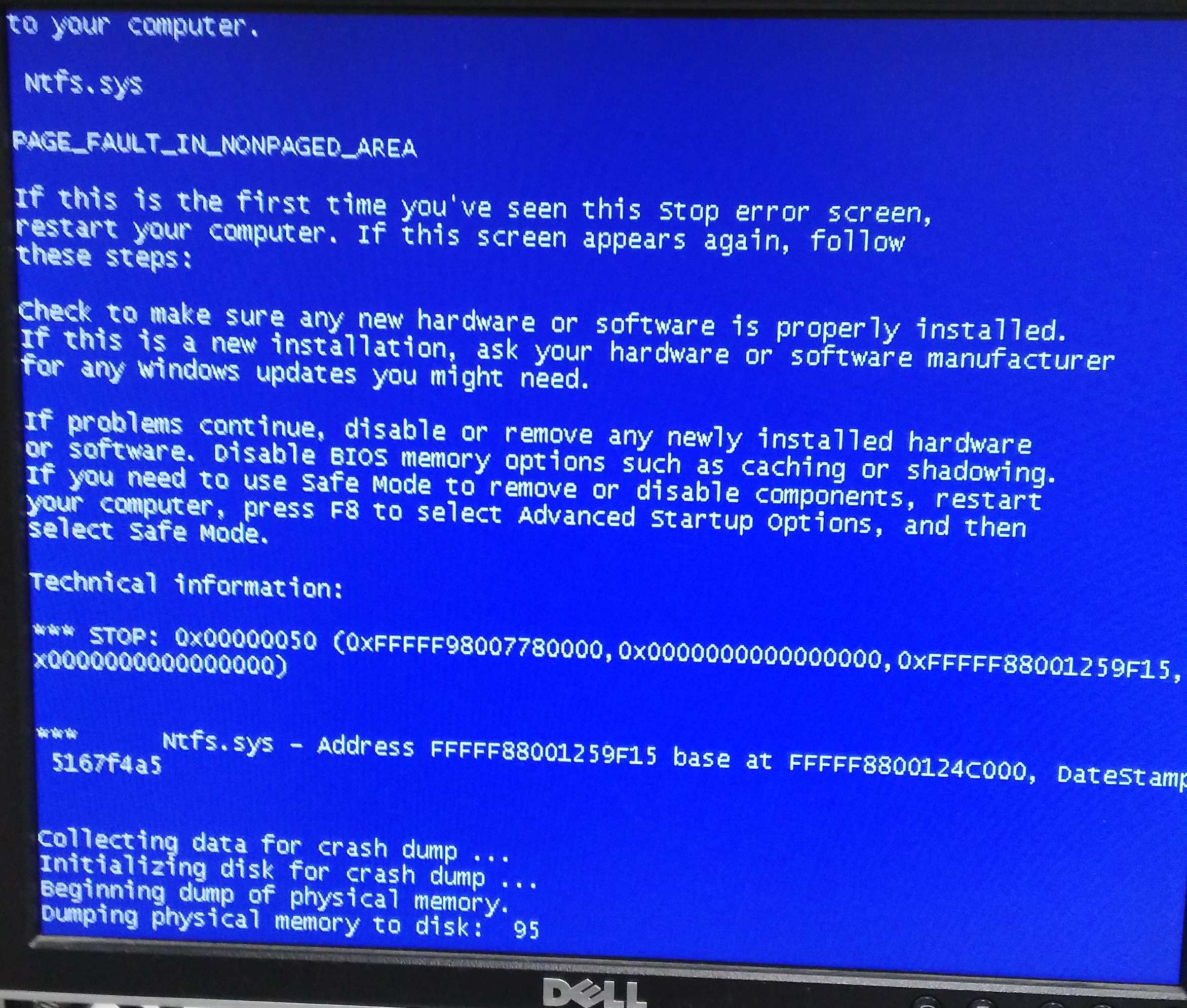
网上搜了半天怀疑是中了病毒硬盘被逻辑锁了,遂将A的硬盘拿下,用转接口连到另一台完好的电脑B上,想要格式化一下。但是A硬盘连上B电脑后,当B电脑的右下角显示USB设备驱动装好后马上就蓝屏了(截图后面附1)。而且我试过好几台电脑,都这样,连上A硬盘就蓝屏。
根据蓝屏信息找到dump文件,用windbg查看信息如附2
实在没碰到过这样妖怪的问题,求大神帮助
附1:
附2,windbg的!analyze -v信息
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
Use !analyze -v to get detailed debugging information.
BugCheck 50, {fffff98014d00000, 0, fffff8800144cc75, 0}
Probably caused by : Ntfs.sys ( Ntfs+ec75 )
Followup: MachineOwner
---------
2: kd> !analyze -v
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
PAGE_FAULT_IN_NONPAGED_AREA (50)
Invalid system memory was referenced. This cannot be protected by try-except,
it must be protected by a Probe. Typically the address is just plain bad or it
is pointing at freed memory.
Arguments:
Arg1: fffff98014d00000, memory referenced.
Arg2: 0000000000000000, value 0 = read operation, 1 = write operation.
Arg3: fffff8800144cc75, If non-zero, the instruction address which referenced the bad memory
address.
Arg4: 0000000000000000, (reserved)
Debugging Details:
ADDITIONAL_DEBUG_TEXT:
Use '!findthebuild' command to search for the target build information.
If the build information is available, run '!findthebuild -s ; .reload' to set symbol path and load symbols.
MODULE_NAME: Ntfs
FAULTING_MODULE: fffff80002062000 nt
DEBUG_FLR_IMAGE_TIMESTAMP: 52e1be8a
READ_ADDRESS: unable to get nt!MmSpecialPoolStart
unable to get nt!MmSpecialPoolEnd
unable to get nt!MmPoolCodeStart
unable to get nt!MmPoolCodeEnd
fffff98014d00000
FAULTING_IP:
Ntfs+ec75
fffff880`0144cc75 488b440af0 mov rax,qword ptr [rdx+rcx-10h]
MM_INTERNAL_CODE: 0
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: VISTA_DRIVER_FAULT
BUGCHECK_STR: 0x50
CURRENT_IRQL: 0
LAST_CONTROL_TRANSFER: from fffff80002152217 to fffff800020d63c0
STACK_TEXT:
fffff880`02199208 fffff800`02152217 : 00000000`00000050 fffff980`14d00000 00000000`00000000 fffff880`02199370 : nt+0x743c0
fffff880`02199210 00000000`00000050 : fffff980`14d00000 00000000`00000000 fffff880`02199370 00000000`00000000 : nt+0xf0217
fffff880`02199218 fffff980`14d00000 : 00000000`00000000 fffff880`02199370 00000000`00000000 fffff880`02199370 : 0x50
fffff880`02199220 00000000`00000000 : fffff880`02199370 00000000`00000000 fffff880`02199370 00000000`00000000 : 0xfffff980`14d00000
STACK_COMMAND: .bugcheck ; kb
FOLLOWUP_IP:
Ntfs+ec75
fffff880`0144cc75 488b440af0 mov rax,qword ptr [rdx+rcx-10h]
SYMBOL_NAME: Ntfs+ec75
FOLLOWUP_NAME: MachineOwner
IMAGE_NAME: Ntfs.sys
BUCKET_ID: WRONG_SYMBOLS
Followup: MachineOwner
---------
2: kd> lmvm nt
start end module name
fffff800`02062000 fffff800`0264e000 nt T (no symbols)
Loaded symbol image file: ntoskrnl.exe
Image path: ntoskrnl.exe
Image name: ntoskrnl.exe
Timestamp: Fri Jan 22 13:06:31 2016 (56A1B8D7)
CheckSum: 00550B0D
ImageSize: 005EC000
Translations: 0000.04b0 0000.04e4 0409.04b0 0409.04e4
 发帖
发帖 与我相关
与我相关 我的任务
我的任务 分享
分享